In 2026, Asia's CISOs and SOC leaders navigate a perfect storm of accelerated digital transformation, hybrid cloud environments and lean security teams stretched across vast geographies. Ransomware attacks continue to surge, with the Asia-Pacific region recording a 59% increase in incidents throughout 2025.
Source: The Managed XDR Global Threat Report, Barracuda Networks 2026
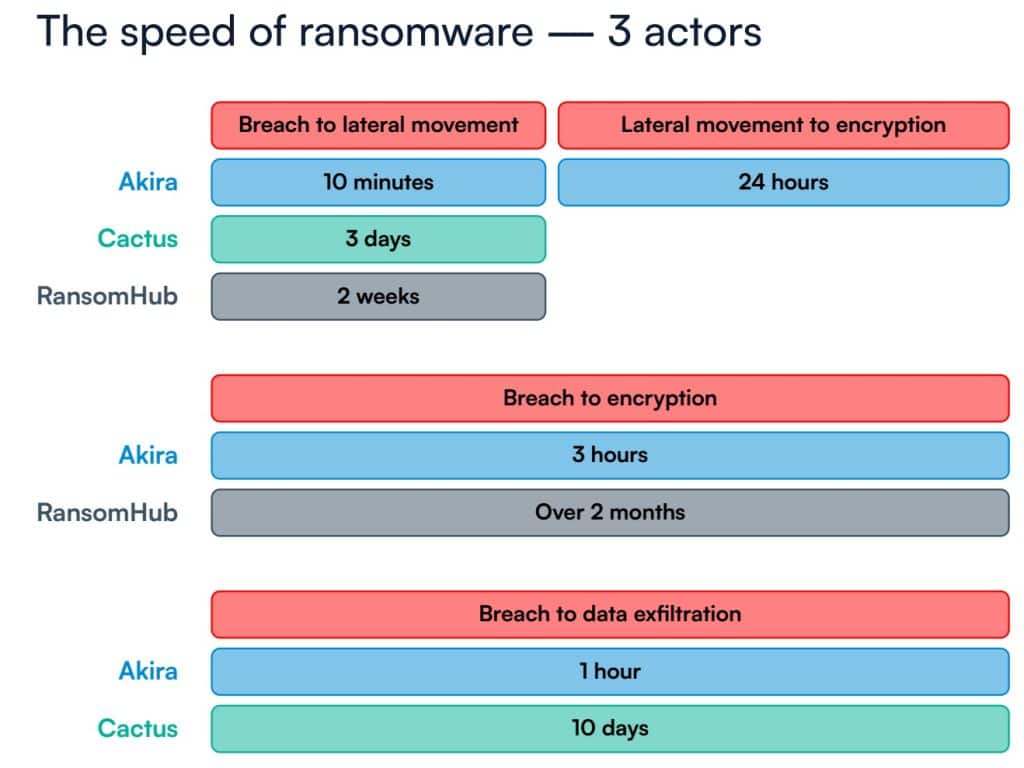
Global data from Barracuda's Managed XDR Global Threat Report, analysing more than two trillion IT events in 2025, reveals that the fastest attacks now compress the breach-to-encryption timeline to just three hours.
IBM's Cost of a Data Breach Report 2025 underscores the financial toll, placing the average ransomware extortion cost at US$5.08 million, even as overall breach costs fell 9% globally to US$4.44 million.
For security leaders, the message is clear: visibility gaps are no longer abstract risks but operational liabilities that attackers exploit with ruthless efficiency.
Tiered expertise meets AI automation
Merium Khalid, director of SOC Offensive Security at Barracuda Networks, has witnessed the transformation firsthand.

"The landscape of a SOC has dramatically changed," she explains. "If you looked back 15 or 20 years ago, you would find a tier 1 SOC with not many experts. Nowadays, it's very tiered, and there are levels of experts within a SOC."
Today's mature SOCs feature dedicated teams for endpoint detection, offensive security, red teaming, and even customer-facing cyber concierge services.
Khalid highlights the role of AI in this evolution. SOCs are automating redundant, low-risk tasks, freeing analysts to focus on advanced incidents. Gartner predicts that by 2026, 50% of SOCs will deploy AI-based decision support, inverting the analyst role from triage operator to strategic supervisor.
In resource-constrained Asian environments, this maturation is not optional; it is essential for maintaining resilience amid rapid cloud adoption and hybrid infrastructure growth.
Top blind spots enabling modern ransomware
Drawing on Barracuda's 2025 telemetry and her incident-response experience, Khalid identifies three critical blind spots.
First come rogue devices: unmonitored endpoints left exposed, providing attackers with quiet footholds for lateral movement. Second are unpatched systems, particularly public-facing firewalls that attract threat actors daily. Third is uneducated staff, still susceptible to phishing despite widespread awareness efforts.
The data is stark. 100% of incidents involved at least one unprotected or rogue endpoint, while 90% of ransomware cases exploited firewalls via a known CVE or a vulnerable account.
Lateral movement, described by Khalid as the clearest red flag, preceded ransomware release in 96% of cases. Sixty-six per cent of incidents involved the supply chain or a third party, up sharply from 45% the previous year.
Reframing security strategy for Asia's hybrid realities
Khalid urges CISOs to proactively reframe their approach.
"Make sure you have routine asset management scans running. Make sure you have a vulnerability management programme set within your organisation as well, where you're patching at a monthly or even at a bi-weekly level." Merium Khalid
Security awareness training must become embedded, not episodic.
In Asia's lean teams managing multi-cloud estates, this means prioritising 24/7 monitoring across every asset. "Having eyes on your data, 24 by 7, 365 is the most important," Khalid stresses.
Bi-weekly patching cadences, combined with quarterly password rotations for admin accounts, close the most exploited vectors without requiring additional headcount.
Correlating events before lateral movement
Security teams must now operate at machine speed. Khalid recommends correlating events across firewalls, servers and endpoints to distinguish legitimate admin activity from compromise. "If you see a brute force activity followed by a risky login and some lateral movement, that's most likely not authorised."
Automated response playbooks have proven decisive. IP blocking at the first sign of suspicious communication, device isolation upon lateral movement detection, and immediate account suspension for risky logins all dramatically shrink dwell time.
In one example, Khalid shares, impossible-travel logins (a user authenticating from China then Canada within minutes) trigger instant suspension and session termination, preventing any meaningful damage.
Eliminating inherited blind spots without adding headcount
Asia's interconnected ecosystems amplify third-party risks. Khalid notes that organisations are "not standalone islands" and recommends SOC-as-a-service models for small and medium-sized businesses lacking internal capacity.
She stresses the importance of having a SOC-as-a-service that continuously monitors assets, including firewalls, servers, e-mail, and endpoints. "It's very important to correlate all the data and have that visibility because if you have one point that is not covered, it's basically an entry point for the threat actor," she explains.
Onboarding needs to be deliberately frictionless, whether in self-service agent deployment, API integrations for cloud assets, or rapid visibility within hours. For lean APAC teams, this model delivers enterprise-grade correlation and response without the overhead of building a full internal SOC.
Prioritising telemetry and shrinking the reaction window
Khalid stresses that endpoint and network telemetry should focus on security-relevant signals: inbound and outbound connections, SSL/VPN activity, running processes and new files.
Continuous device scanning flags malicious artefacts immediately. Automated responses turn minutes of potential damage into seconds of containment.
"Even reducing it from 10 minutes to a second or a minute really saves the organisation from a lot of reputational damage," she adds.
Auditing invisible blind spots operationally
Practical remediation begins with rhythm. Monthly vulnerability scans and rogue-device audits produce prioritised reports focused on critical and high-severity issues. Quarterly account audits remove stale credentials belonging to former employees.
These low-effort disciplines, delivered via managed services, maintain hygiene without disrupting daily operations.
Behavioural baselines and XDR anomaly detection
Machine learning within XDR platforms builds organisation-specific baselines. At Barracuda, she reveals that: "We use 90 days of data to continuously train our models and continuously learn the activity in your environment." She explains that what may be normal for one organisation is not normal for another.
Khalid highlights red flags such as logins at unusual hours, new device IDs or connections from unfamiliar countries and ISPs.
"We have over 30 different features that are integrated into our machine learning model that look at baselining and anomaly detections and anything that's out of the normal." Merium Khalid
These tuned rules flag malicious use of legitimate tools before lateral movement escalates.
Integrating AI-powered autonomous response with human oversight
Khalid is unequivocal about the future: automation precedes agentic AI. "Automation should be adopted first. Automation is the first stage to using AI."
Low-risk tasks such as IP blocking, device isolation and account suspension are ideal candidates for autonomous handling, while human analysts retain oversight of high-risk ransomware incidents. Barracuda's SOC already operates at this higher maturity level, combining people-powered service with AI-enhanced detection.
"People power us, but AI enhances us," she says. "When you call our SOC, you're going to get someone on the phone. We're using AI to make sure we're protecting our customers because threat actors are also using AI."
Choosing the right SOC partner
When evaluating SOC-as-a-service providers, maturity matters. Khalid advises looking beyond single-tier operations to multi-tiered teams boasting defensive and offensive certifications.
"Would you want to go with a SOC that is only 1 tier… Or do you want to go with a SOC that's multi-tiered, has industry standard level certifications?" she queried rhetorically.
Her recommendation: "When you're choosing a SOC or a SOC-as-a-service, look at the maturity. Look at how it's built. Look at the different people or the different types of certifications that they have."
Advice for Asia's security leaders
Khalid's closing counsel is blunt yet pragmatic. "In terms of getting attacked or breached, it's not a matter of if you're going to get attacked or breached. It's a matter of when you're going to get attacked or breached."
The imperative is clear: adopt a proactive posture with robust guardrails, continuous monitoring and layered defences. Reactive spending after an incident creates enormous budgets that could have been avoided through earlier investment.
For CISOs and SOC heads across Asia in 2026, the path forward is not about chasing every new threat but systematically closing the known blind spots that modern ransomware continues to exploit.
With the right visibility, automation and partnerships, lean teams can turn defence from a cost centre into a genuine enabler of resilient digital growth.



