Technological performance alone is no longer enough to judge a cybersecurity vendor: Sophos’ new global research shows that trust has become a make‑or‑break factor in how organisations select and manage their security partners.
In the Cybersecurity Trust Reality 2026 report—a vendor‑agnostic study of 5,000 organisations across 17 countries—only 5% of respondents say they have full trust in their cybersecurity vendors, while 95% report lacking complete confidence in at least some of their suppliers.
The findings position trust not as a marketing talking point but as a measurable risk dimension that shapes both operational resilience and board‑level decisions.
A trust deficit in the security stack
Source: Sophos 2026
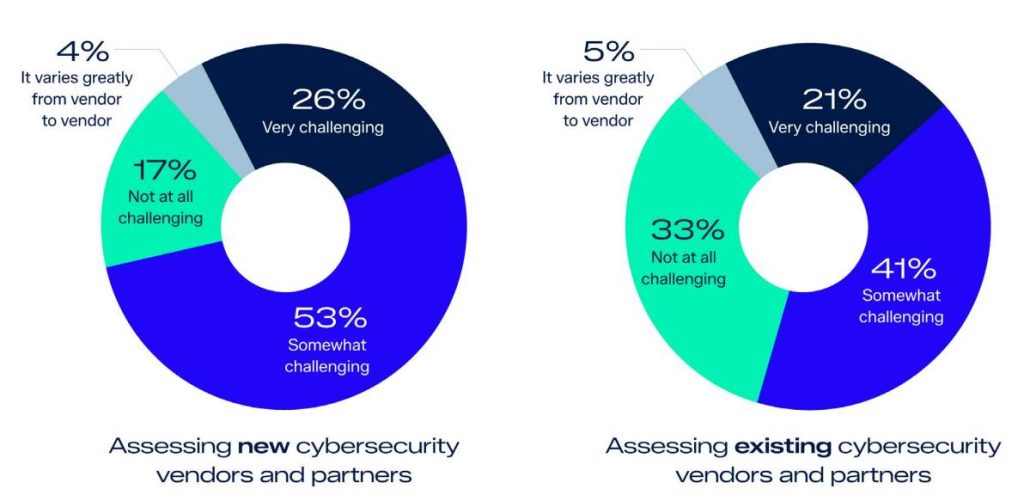
At a time of escalating cyber threats, regulatory scrutiny and AI‑driven tools, the survey reveals that trust in cybersecurity vendors is fragile, hard to measure and poorly understood. Nine‑in‑ten organisations (79%) say they struggle to assess the trustworthiness of new cybersecurity partners, and 62% find it difficult even for existing vendors.
Over half (51%) report increased anxiety about the likelihood of a significant cyber incident because of this trust gap, a signal that the uncertainty around vendor practices is actively feeding into their risk posture.
For CISOs, this plays out as slower decision‑making, higher vendor turnover and operational friction. Teams hesitate to adopt new tools, rotate stacks or decommission legacy systems when they cannot be confident that the underlying providers are themselves secure and transparent.
The report underscores that effectiveness is no longer judged solely by detection rates or time‑to‑remediate metrics; it is also shaped by how much the organisation trusts the vendor’s internal controls, incident response maturity and ability to stay aligned with evolving regulatory expectations.
What drives trust in cybersecurity vendors?
The research identifies verifiable security artifacts—such as independent assessments, recognised certifications and documented operational maturity—as the strongest single driver of vendor trust.
CISOs place the highest value on transparency during incidents (timely, clear communication and remediation actions) and consistent technical performance, while boards and senior leaders lean more heavily on third‑party validation, such as audits and analyst‑rated performance [Sophos 2026]. The common thread is that organisations want evidence‑backed transparency, not aspirational statements or opaque “we’re secure” claims Sophos.
“Trust is not an abstract concept in cybersecurity, it’s a measurable risk factor,” said Ross McKerchar, CISO at Sophos. “When organisations can’t independently verify a vendor’s security maturity, transparency, and incident handling practices, that uncertainty flows directly into boardrooms and security strategies.”
That line of thinking reflects a broader shift in the GRC space, where regulators increasingly expect firms to demonstrate due diligence in third‑party and AI‑enabled risk management [IDC guidance on GRC and AI‑governance].
Trust as a compliance and AI‑governance imperative
The report also highlights how AI is reshaping what trust looks like in cybersecurity. As AI becomes embedded in tools, services and workflows, organisations are no longer just asking whether a solution is technically effective; they are also evaluating whether AI is deployed responsibly, with clear governance, explainability and safeguards against bias or misuse.
Phil Harris, research director, governance, risk and compliance solutions at IDC, noted that “with regulatory pressure increasing globally, organisations must be able to demonstrate due diligence in vendor selection—especially where AI is involved. Trust is shifting from a marketing message to a defensible compliance requirement.”
For CISOs, this means that proving trust has moved from a nice‑to‑have to a core accountability. Respondents cited a lack of accessible, sufficiently detailed information as the primary barrier to making confident trust assessments, underscoring a gap between vendor claims and the evidence security teams actually need. “CISOs are being asked to prove trust, not assume it,” added McKerchar.
“Cybersecurity providers must do the same. Respondents to the survey cited a lack of accessible, sufficiently detailed information as the primary barrier to making confident trust assessments. Trust must be earned continuously through transparency, accountability, and independent validation.”
Ultimately, the Cybersecurity Trust Reality 2026 findings elevate trust from a brand‑level attribute into a strategic imperative: a factor that shapes technology choices, regulatory posture, board‑level risk appetite and the resilience of the entire security ecosystem.