The second-half 2025 CyOps ECHO Report by Cynet highlights alarming trends in cyber threats where AI-driven attacks and the rise of “cyber cartels” are collapsing exploitation timeframes from days to mere hours. This report is particularly pertinent for Chief Information Security Officers (CISOs) in Asia, as they navigate complex cybersecurity challenges amid escalating global threats.
The report draws on insights from Cynet’s incident response team, revealing that more than 40% of vulnerabilities added to the CISA KEV (Known Exploited Vulnerabilities) list were confirmed zero-days.
Attackers are increasingly exploiting these vulnerabilities nearly instantaneously using AI automation. Key tactics identified include advanced social engineering techniques that manipulate users into granting access, and accelerated malware development that allows even less skilled adversaries to create sophisticated malicious software.

"Zero-day response is the new normal," states MacKenzie Brown, vice president of threat intelligence strategy at Cynet. "“When adversaries weaponise vulnerabilities in hours, traditional patching and scoring methods don’t hold up."
This new reality highlights the inadequacy of traditional patching methods, forcing organisations to rely on actionable intelligence that assesses the likelihood of exploitation.
For CISOs in Asia, rapid awareness of emerging vulnerabilities and the potential for exploitation is critical to maintaining robust cybersecurity measures.
The report further discusses the evolution of cyber cartels, where attackers collaborate like corporate entities—coordinating operations, sharing resources, and now employing advanced tactics like “identity-bending” social engineering. Instead of brute-force attacks, they are manipulating legitimate collaboration tools, such as Microsoft Teams, to obtain access without raising suspicion. This shift necessitates a greater emphasis on monitoring user behaviour and collaboration features.
For CISOs in Asia, who often face unique geopolitical and regulatory challenges, these insights underscore the need for enhanced security frameworks. Strategies should incorporate continuous monitoring, behavioural analysis, and rapid response capabilities to effectively address the evolving tactics used by adversaries.
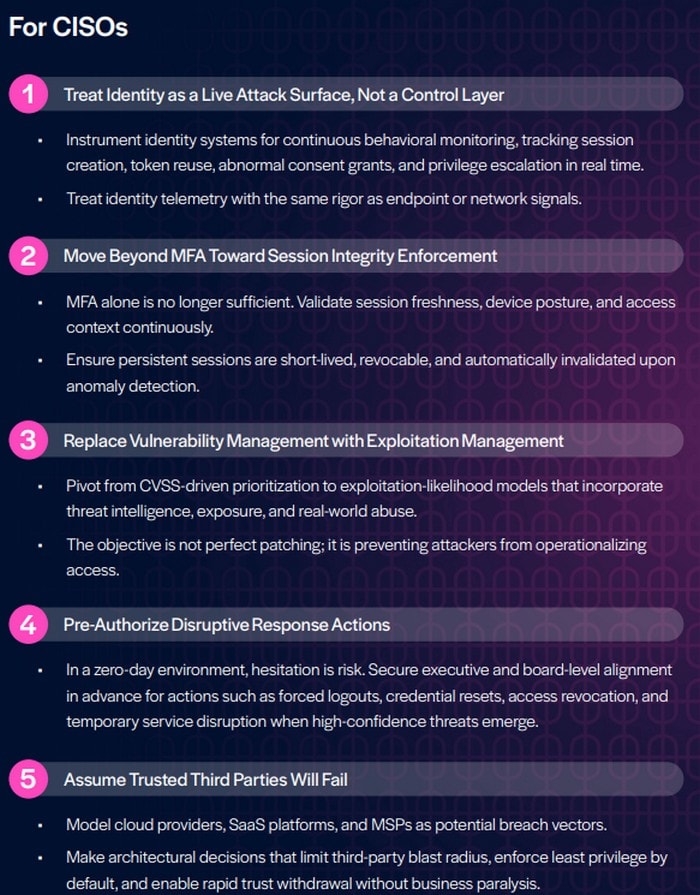
The importance of a proactive and agile security posture is clear. By prioritising real-time visibility and trust-revocation capabilities, organisations can better defend against the increasingly sophisticated tactics of cyber adversaries.



