The latest "Open Source Security and Risk Analysis" (OSSRA) report from Black Duck provides crucial insights into the dramatically changing landscape of open source software vulnerabilities, with significant implications for CISOs across Asia in 2026.
Source: Open Source Security and Risk Analysts report, Black Duck 2026
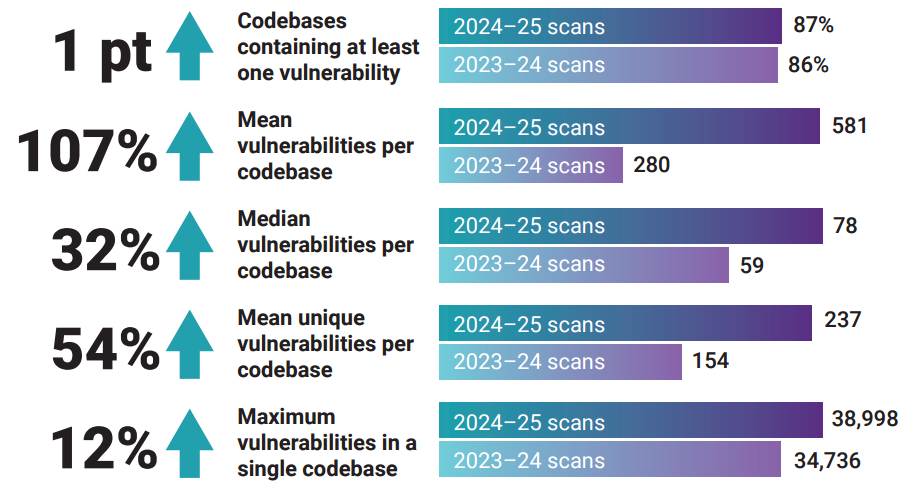
The report reveals a staggering 107% increase in the average number of vulnerabilities per codebase, as the proliferation of AI-assisted code creation accelerates the introduction of new risks.
With open source components now present in 98% of codebases globally, CISOs must grapple with the realities of third-party risks embedded within their applications.
The OSSRA report analysed nearly 950 codebases across 17 industries, highlighting that AI's integration into software development has not only inflated the volume of code but also exacerbated risk factors such as licensing conflicts and operational vulnerabilities.
The data indicates that 68% of audited codebases contain conflicts regarding open source licenses, marking the highest rate in the report's history. This represents a significant legal risk, putting additional pressure on security teams to ensure compliance amid evolving regulations, such as the EU Cyber Resilience Act. As many Asian enterprises embrace open source technologies, companies must monitor their software supply chains closely to navigate these complexities.
The report warns that governance structures have not kept pace with AI adoption; only 24% of organisations conduct comprehensive evaluations for AI-generated code regarding intellectual property (IP), licensing, security, and quality. This raises alarms for CISOs who must ensure robust governance frameworks to safeguard their organisations against potential legal repercussions.
The acceleration of code creation has also led to an increased attack surface that can be exploited by malicious actors. As AI tools proliferate, attackers are finding new pathways to inject vulnerabilities through third-party dependencies and unregulated AI-generated content.
"Every organisation is dependent on the security practices of open source maintainers, the licensing decisoons made for open source projects, and the continued viability of those projects' components." OSSRA 2026
For CISOs in Asia, this underscores the urgent need for enhanced visibility into their software environments to establish trust with stakeholders and comply with emerging regulations.
"Visibility has become the new currency of trust," says Jason Schmitt, CEO of Black Duck. He emphasises that understanding the full composition of software—not just openly licensed components—is essential for managing these risks effectively.



