The Tenable report, Cloud and AI Security Risk Report 2026, reveals a stark reality: organisations are struggling to manage cyber risks effectively as the pace of AI adoption and third-party code integration accelerates beyond their ability to secure it.
The study reveals 86% of organisations have implemented third-party code packages containing critical vulnerabilities, transforming the software supply chain into a persistent source of exposure.
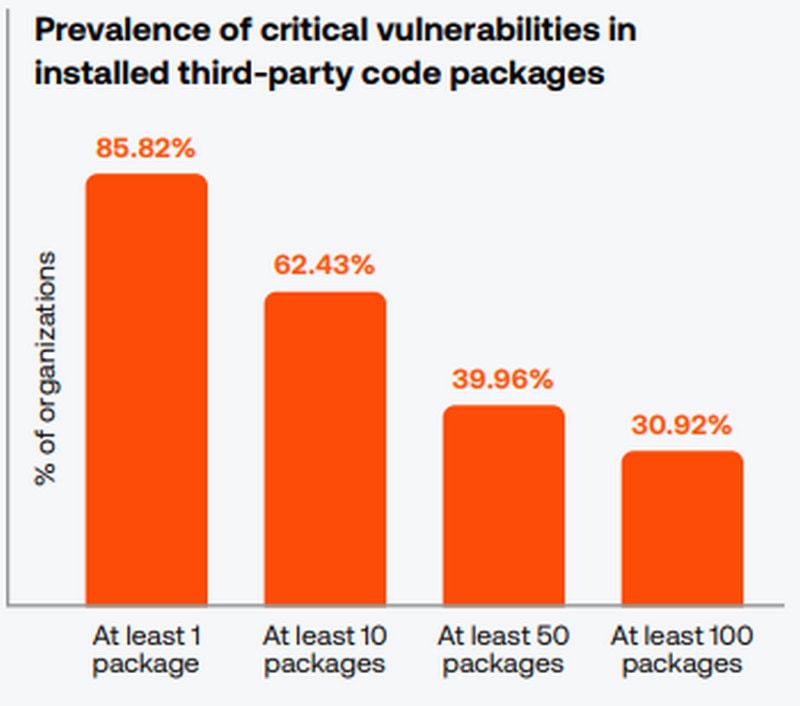
Source: Tenable Cloud and AI Security Risk Report 2026

“The AI exposure gap represents a significant risk, as organisations must contend with inherited vulnerabilities faster than they can remediate them,” stated Liat Hayun, senior vice president of product management and research at Tenable.
This is particularly concerning in Asia, where rapid technological advancements and digital transformation initiatives are prevalent, making robust risk management even more critical.
Moreover, the report indicates that 65% of organisations expose high-value assets due to neglected cloud credentials—termed "ghost" secrets. With 18% of organisations granting AI services administrative permissions that often go unmonitored, the potential for exploitation becomes alarmingly high.
This situation is compounded by the fact that non-human identities—such as AI agents and service accounts—now pose 52% more risk than traditional human users.
For CISOs, the implications are clear. The lack of visibility and governance around AI-integrated systems necessitates a shift in focus toward comprehensive identity controls and enhanced security postures. The report advocates for the implementation of least privilege access for AI roles and the dissolution of static secret exposure to mitigate risk.
As organisations actively integrate AI into their operations, the report provides actionable insights for reducing risks across cloud and AI environments. Redefining exposure management practices to encompass software vulnerabilities, identity risk, and cloud security gaps is essential in this landscape marred by supply chain vulnerabilities.
By unifying visibility across code packages, cloud environments, and identity access, CISOs can begin to manage actual business risks rather than merely addressing accumulated security debt.